Hexis
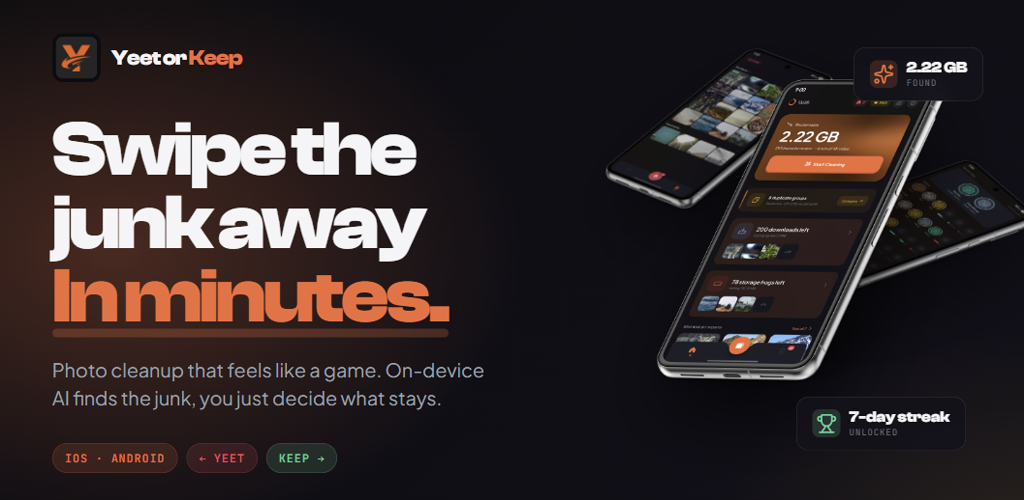
<h2>Overview</h2><p>Automating behavior inside a real-time 3D environment is a harder engineering problem than it looks. The system has to read the world around it, plan paths through terrain that changes, execute actions with human-like timing, and do all of this at 20 ticks per second without dropping frames.</p><p><strong>Hexis</strong> is a platform I built from scratch to solve that problem. It runs inside Minecraft as a Fabric mod, but the engineering spans 5 programming languages and 3 foreign function interface bridges. A Rust pathfinder computes routes through 3D terrain via JNI. A spring-damper physics engine controls camera movement so it looks natural. Users write Lua scripts to define what the system does. And a full SaaS web platform handles licensing, payments, and mod delivery.</p><p>What started as a personal project turned into a real product: 300+ registered users, paying customers, and a security architecture I had to rebuild under pressure after a real-world crack.</p><hr><h2>At a Glance</h2><ul><li><p><strong>5</strong> Programming languages</p></li><li><p><strong>3</strong> FFI bridges (Java <-> Rust, Java <-> C, Java <-> Lua)</p></li><li><p><strong>300+</strong> Beta users in the first 3 months</p></li><li><p><strong>790</strong> Commits across 5 repositories</p></li><li><p><strong>~120K</strong> Lines of source code</p></li></ul><hr><h2>Architecture</h2><div data-image-grid="" data-columns="2" class="image-grid" style="display: grid; grid-template-columns: repeat(2, 1fr); gap: 1rem;"><img src="https://vivujyp67aiffgjd.public.blob.vercel-storage.com/projects/images/content-image-1775507329118-VdRGx9uLqbntlK2y3OPV5qMyiA0o1W.png" alt="Hexis Architecture Non Technical - White Text.png" style="width: 100%; height: 250px; border-radius: 0.75rem; object-fit: cover;"></div><p>The system is split across five repositories, each handling a distinct concern:</p><p><strong>Hexis Mod (Java + Rust + C)</strong><br>The core client-side mod. Contains the scripting engine, pathfinding system, mining system, combat system, camera physics, GUI rendering, and security layer. Native code is loaded via JNI at runtime.</p><div data-image-grid="" data-columns="2" class="image-grid" style="display: grid; grid-template-columns: repeat(2, 1fr); gap: 1rem;"><img src="https://vivujyp67aiffgjd.public.blob.vercel-storage.com/projects/images/content-image-1775502390826-rGY7zBtUkBqliXawdveO6T6mfPfGjU.png" alt="image.png" style="width: 100%; height: 250px; border-radius: 0.75rem; object-fit: cover;"></div><p><a target="_blank" rel="noopener noreferrer" href="https://usehexis.com"><strong>Hexis Website (Next.js 15 + TypeScript + PostgreSQL)</strong></a><br>The SaaS platform. Handles user authentication (Google/Discord OAuth), Stripe payments, license management, mod downloads via Cloudflare R2, and an admin dashboard with encrypted log analysis.</p><p><a target="_blank" rel="noopener noreferrer" href="https://docs.usehexis.com"><strong>Hexis Docs (Docusaurus)</strong></a><br>User-facing API documentation for the Lua scripting system. Covers all 20+ API libraries with examples.</p><div data-image-grid="" data-columns="2" class="image-grid" style="display: grid; grid-template-columns: repeat(2, 1fr); gap: 1rem;"><img src="https://vivujyp67aiffgjd.public.blob.vercel-storage.com/projects/images/content-image-1775502540637-lBDSDeEoE3g2a1wjb8QVjIKFI1lteH.png" alt="image.png" style="width: 100%; height: 250px; border-radius: 0.75rem; object-fit: cover;"></div><p><strong>Hexis Bot (JavaScript)</strong><br>Discord bot for community support, ticketing, and moderation.</p><div data-image-grid="" data-columns="2" class="image-grid" style="display: grid; grid-template-columns: repeat(2, 1fr); gap: 1rem;"><img src="https://vivujyp67aiffgjd.public.blob.vercel-storage.com/projects/images/content-image-1775503364474-MwIaDE6UZ2tIMkkHoH2nApOADhTOJ3.png" alt="Screenshot 2026-04-06 122021.png" style="width: 100%; height: 250px; border-radius: 0.75rem; object-fit: cover;"></div><p><strong>Hexis Decryptor (C)</strong><br>Internal admin tool for analyzing encrypted telemetry logs.</p><div data-image-grid="" data-columns="2" class="image-grid" style="display: grid; grid-template-columns: repeat(2, 1fr); gap: 1rem;"><img src="https://vivujyp67aiffgjd.public.blob.vercel-storage.com/projects/images/content-image-1775503425461-tVLVLrJbCUz4q5Q3HeQqVFuySOuNLX.png" alt="image.png" style="width: 100%; height: 250px; border-radius: 0.75rem; object-fit: cover;"></div><h3>Cross-Language Integration</h3><p>Most of the complexity lives in how these languages talk to each other:</p><ul><li><p><strong>Java to Rust (JNI)</strong><br>The A* pathfinder runs in native Rust for performance. Java serializes the world state into a flat buffer, passes it across the JNI boundary, and Rust returns the computed path. This dropped pathfinding from 800ms+ in pure Java to under 100ms.</p></li><li><p><strong>Java to C (JNI)</strong><br>The security layer runs in native C. License signature verification (Ed25519), parameter decryption (AES-256-CBC), and tamper detection all execute outside the JVM where they're harder to reverse engineer.</p></li><li><p><strong>Lua to Java (LuaJ)</strong><br>Users write Lua scripts that call into Java through a sandboxed API. Each script runs in its own VM with access only to whitelisted functions. No filesystem access, no network access, no raw Java reflection.</p></li></ul><hr><h2>The Algorithms</h2><p>The hardest part of this project wasn't the website or the GUI. It was teaching the system to move like a person would.</p><h3>Pathfinding</h3><p>I implemented A* on a 3D voxel grid in Rust, connected to Java via JNI. The pathfinder handles jumps, drops, water, slabs, stairs, and elevation changes. It uses a binary heap with bucket tiebreaking for the open set and a 3-tier caching system (block state cache, precomputed walkability per chunk, penalty lookups) to minimize world queries during search.</p><p>The result: sub-100ms path computation for distances over 150 blocks.</p><p>I got here by being wrong first. My initial implementation used Dijkstra's algorithm in pure Java. It worked, but it searched exhaustively outward rather than toward the goal, slow and wasteful. Switching to A* with a Euclidean heuristic and moving the computation to native Rust solved both problems.</p><p>Then I made a different kind of mistake. I spent days writing ~700 lines of custom path compression logic to smooth raw A* output into walkable waypoints. It worked, but it was over-engineered and brittle. Later I found the Ramer-Douglas-Peucker algorithm, a well-proven technique that does the same thing in roughly 200 lines with better results. The lesson: before you write something from scratch, check whether someone already solved it better.</p><h3>Camera Physics</h3><p>All programmatic camera rotation passes through a spring-damper physics engine. Instead of snapping the camera to a target angle, the system simulates a spring pulling toward the target with damping to prevent oscillation. Four context-specific profiles (navigation, combat, mining, idle) tune the spring stiffness, damping ratio, and noise characteristics for different activities.</p><p>On top of the physics, every rotation is snapped to GCD-aligned increments that match real mouse sensitivity values, and Gaussian noise is injected into timing and aim points. The goal: camera movement that is statistically indistinguishable from a human player.</p><h3>What 20 Lines of Lua Actually Does</h3><p>A user writes this:</p><pre><code class="language-lua">hexis.script({ name = "Mob Hunter", version = "8.0", category = "Combat" })
local config = hexis.config({ mob_type = hexis.config.dropdown("Mob Type", { {"zombie", "Zombie"}, {"wolf", "Wolf"}, {"enderman", "Enderman"} }, "wolf"), radius = hexis.config.slider("Search Radius", 16, 64, 32, 8), range = hexis.config.slider("Attack Range", 2.0, 4.0, 3.0, 0.5), })
function hexis.main() while true do hexis.combat.hunt({ type = config.mob_type, search_radius = config.radius, attack_range = config.range, }) hexis.wait(1.0) end end </code></pre><p>Behind those 20 lines, the system auto-generates a GUI with dropdowns and sliders from the config declaration, finds the nearest matching entity using spatial queries, computes an A* path through 3D terrain via native Rust, navigates with spring-damper camera physics, targets the entity with hitbox-aware aim selection, attacks with GCD-snapped humanized rotations, and handles stuck detection, repath, and timeout recovery automatically.<br></p><p>The API is designed so that the complexity stays in the engine and the user only expresses intent.</p><hr><h2>The Security Incident</h2><p>Early in development, I left portions of the security logic unobfuscated and didn't enforce signature length validation on the license verification path. A reverse engineer exploited both: they set up a local HTTPS server with a DNS redirect and distributed a cracked version using a fake 4-byte Ed25519 signature that passed the incomplete validation.</p><p>The root cause was shipping before the security architecture was solid. I knew it needed more work, but the pressure of having paying customers waiting pushed me to release early.</p><p>The response was systematic:</p><ul><li><p>Enforced strict signature length validation on all cryptographic paths</p></li><li><p>Implemented "math entanglement", 20 critical algorithm parameters are encrypted server-side with AES-256-CBC, decryptable only with the real Ed25519-verified key. A fake server can return valid-looking JSON, but it can't produce a real signature, so it can't decrypt the parameters that make the algorithms work.</p></li><li><p>Added per-download dual-layer watermarking for leak tracing</p></li><li><p>Deployed native tamper detection in a watchdog thread using JVMTI agent detection</p></li></ul><p>The crack is dead. But the lesson about shipping security half-finished, especially with paying customers, is one that shaped every architectural decision I made afterward.</p><hr><h2>The Discord Bot Incident</h2><p>I built an AI-powered chatbot for the community Discord server to handle tickets, answer common questions, and assist with moderation. It worked well until users discovered they could craft messages that manipulated the bot through prompt injection, causing it to produce unintended responses and trigger server-wide pings.</p><p>I took it offline, reworked the input sanitization pipeline and system prompt constraints, and redeployed it with proper guardrails. It was a firsthand lesson in the importance of treating LLM inputs as untrusted, the same principle as sanitizing SQL or HTML, applied to a newer attack surface.</p><hr><h2>Lessons Learned</h2><p><strong>Research before you build.</strong> Two of my biggest technical detours (Dijkstra's algorithm, the custom path compression) would have been avoided with a few more hours of reading before writing code.</p><p><strong>Security is architecture, not a feature.</strong> I learned this the hard way. Design it in from the start, or someone will find what you left open.</p><p><strong>Shipping something real teaches you more than any tutorial.</strong> Hexis has 300+ users, a recovered security incident, a prompt injection postmortem, and an architecture I rebuilt under pressure. That experience is more formative than anything I could have gotten from coursework alone.</p><hr><h2>Access</h2><ul><li><p><strong>Website:</strong> <a target="_blank" rel="noopener noreferrer" href="http://usehexis.com">usehexis.com</a></p></li><li><p><strong>Source Code:</strong> <a target="_blank" rel="noopener noreferrer" href="https://github.com/Andrew-Forster/hexis-mod">github.com/Andrew-Forster/hexis-mod</a> | <a target="_blank" rel="noopener noreferrer" href="https://github.com/Andrew-Forster/hexis-website">github.com/Andrew-Forster/hexis-website</a></p></li><li><p><strong>API Documentation:</strong> <a target="_blank" rel="noopener noreferrer" href="http://docs.usehexis.com">docs.usehexis.com</a></p></li><li><p><strong>Portfolio:</strong> <a target="_blank" rel="noopener noreferrer" href="http://andrewjf.com">andrewjf.com</a></p></li></ul><p>Hexis requires Minecraft 1.21 with the Fabric mod loader. Users purchase a license through the website, authenticate via Discord or Google, and download the mod directly from the dashboard.</p><p></p>